OPC UA Client Driver
Not counted towards your tag license limit.
OPC UA is an alternative communication protocol to OPC CLASSIC, which used DCOM for communication between a client and a server. VTScada still supports the existing OPC CLASSIC driver.
Unlike OPC CLASSIC, OPC UA, does not rely on third-party "OPC-tunnellers" to act as proxies between the client and server. An OPC UA server may run on a remote computer or be embedded in a smart device and can run on a variety of operating systems. Because there are a limited number of OPC UA products, a tunneller can be used to connect OPC UA clients to an OPC CLASSIC server.
Do not proceed with OPC UA Client Driver configuration until you have read the related information in the topic, OPC UA Support & Security
If both client and server are using OPC UA, the only additional configuration necessary is to ensure that firewalls allow the correct ports to be opened and that trust is established between the server and client. The port(s) in use are defined by the OPC UA server.
The "None" security policy permits communication without encryption or message signing (no confidentiality or integrity). This should only be selected for testing or when the connection is otherwise protected by external means, such as a VPN between the VTScada system and the OPC UA server.
Where encryption or cryptographic signing of communication is desired (recommended), a trusted certificate is required at both the OPC UA server and the VTScada OPC UA Client driver to verify identity.
Unlike many other drivers, the OPC UA Client does not use a Port tag to communicate with its device (OPC UA server). Due to the nature of the binary protocol, the OPC UA Client has port handling built-in.
If VTScada and the UA server are out of time synchronization by more than 5 minutes, the connection will not be made. The driver will return a 520 error, indicating a large time differential.
The OPC UA Client Driver Statistics Dialog widget provides an "Endpoints" button, which when pressed, will display the list of OPC UA Server Endpoint information that is retrieved by the driver and held internally. This information may be helpful when trying to diagnose connection issues or user authentication problems.
Importing tags from an OPC UA device
Not all OPCUA nodes are considered to be tags, so not all can be imported. The Tag Browser's Import tool will place properties of tags inside the I/O tag where possible instead of bringing them in as separate IO tags.
If the latter functionality is desired, the user will have to create their own independent I/O tags for this purpose.
Importing tags with the same display name is not supported. It is recommended that you review your tag structures and make sure no duplicates exist before attempting to import.
OPC UA Addressing - I/O address formats.
Communication Driver Log-Enabled Variables - Log Enabled Variables.
The ID tab of every tag includes the same common elements: Name, Area, Description, and Help ID.
Name:
Uniquely identifies each tag in the application. If the tag is a child of another, the parent names will be displayed in a separate area before the name field.
You may right-click on the tag's name to add or remove a conditional start expression.
Area
The area field is used to group similar tags together. By defining an area, you make it possible to:
- Filter for particular tag groups when searching in the tag browser.
- Link dial-out alarm rosters to Alarm tags having a particular area.
- Limit the number of tags loaded upon startup.
- Filter the alarm display to show only certain areas.
- Filter tag selection by area when building reports.
When working with Parent-Child tag structures, the area property of all child tags will automatically match the configured area of a parent. Naturally, you can change any tag's area as required. In the case of a child tag, the field background will turn yellow to indicate that you have applied an override. (Orange in the case of user-defined types. Refer to Configuration Field Colors).
To use the area field effectively, you might consider setting the same Area for each I/O driver and its related I/O tags to group all the tags representing the equipment processes installed at each I/O device. You might also consider naming the Area property for the physical location of the tag (i.e. a station or name of a landmark near the location of the I/O device). For serial port or Roster tags, you might configure the Area property according to the purpose of each tag, such as System or Communications.
You may define as many areas as you wish and you may leave the area blank for some tags (note that for Modem tags that are to be used with the Alarm Notification System, it is actually required that the area field be left blank).
To define a new area, type the name in the field. It will immediately be added. To use an existing area, use the drop-down list feature. Re-typing an existing area name is not recommended since a typo or misspelling will result in a second area being created.
There is no tool to remove an area name from VTScada since such a tool is unnecessary. An area definition will exist as long as any tag uses it and will stop existing when no tag uses it (following the next re-start).
Description
Tag names tend to be brief. The description field provides a way to give each tag a human-friendly note describing its purpose. While not mandatory, the description is highly recommended.
Tag descriptions are displayed in the tag browser, in the list of tags to be selected for a report and also on-screen when the operator holds the pointer over the tag’s widget. For installations that use the Alarm Notification System, the description will be spoken when identifying the tag that caused the alarm.
The description field will store up to 65,500 characters, but this will exceed the practical limits of what can be displayed on-screen.
This note is relevant only to those with a multilingual user interface:
When editing any textual parameter (description, area, engineering units...) always work in the phrase editor. Any changes made directly to the textual parameter will result in a new phrase being created rather than the existing phrase being changed.
In a unilingual application this makes no difference, but in a multilingual application it is regarded as poor practice.
Help Search Key
Used only by those who have created their own CHM-format context sensitive help files to accompany their application.
Server List
Select (or create) a named server list.
OPC UA Client Driver properties Connection tab
Use this tab to supply the address of the server.
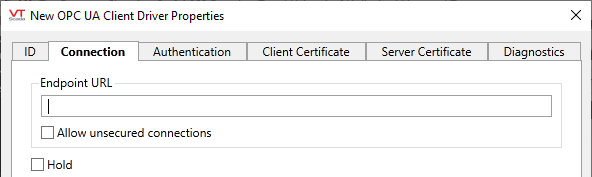
Endpoint URL
The address of a server using the OPC UA binary encoding is known as an Endpoint URL and is expressed as:
opc.tcp://server:port/path
(see: Server Addressing in the topic, OPC UA Addressing)
Select the type of transport security to be used between the VTScada OPC UA Client driver and the OPC UA server.
Enforce Secure Connection
Always connect using the most secure endpoint available (excludes None).
Prefer Secure Connection
Connect using the most secure endpoint available but allow fallback to None as a last resort.
Use Unsecure Connection
Strictly connect using the "None" security policy. If unavailable, the connection will fail.
The "None" security policy permits communication without encryption or message signing (no confidentiality or integrity). This should only be selected for testing or when the connection is otherwise protected by external means, such as a VPN between the VTScada system and the OPC UA server.
Where encryption or cryptographic signing of communication is desired (recommended), a trusted certificate is required at both the OPC UA server and the VTScada OPC UA Client driver to verify identity.
Hold
Select this to have I/O tags attached to the driver hold their last value in the event of a communication failure. If not selected, tags will have their value set to invalid on a communication failure.
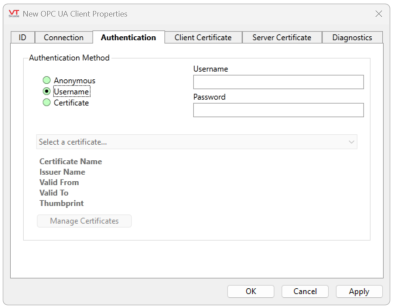
OPC UA Client Driver properties Authentication tab
Refer to OPC UA Support & Security for more detail on required security configuration.
Fields within this tab are enabled according to your selection of authentication method:
Anonymous
When authentication is set to Anonymous, no other fields are enabled.
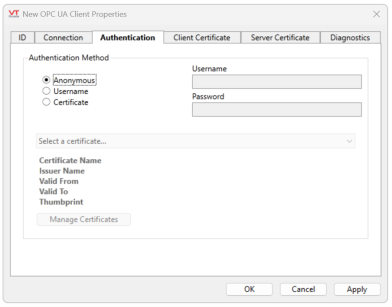
Username
Username and Password fields are enabled.
Certificate
'Select a certificate...' drop-down and 'Manage Certificates' button are enabled.
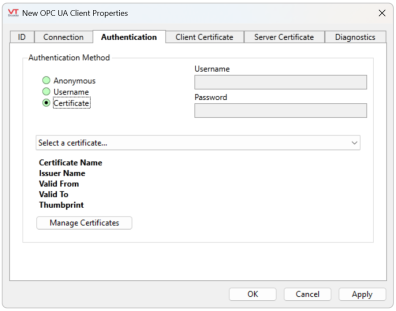
The 'Select a certificate...' droplist displays a list of available certificates in the current user's Personal Windows certificate store. Selecting the 'Manage Certificates' button will load the Certificate Management UI, where the user may add, update, delete or renew certificates.
If the certificate selected is set to expire in less than 30 days, the expiry date text in the 'Valid To' field will be orange in color and red if it has expired.
Certificates created through the Certificate Management UI will also have an automatically created URL and DNS entry. The URL is derived from the application GUID, making it unique to your instance of VTScada. The DNS entry contains the host name of the workstation on which you are creating this certificate (not the fully qualified domain name (FQDN)). These are used visibly in the certificate's Subject Alternative Names (SAN).
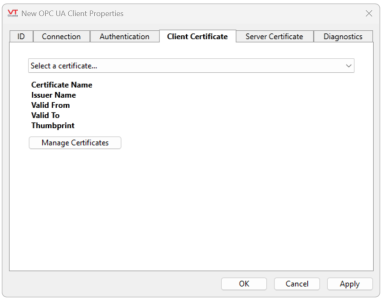
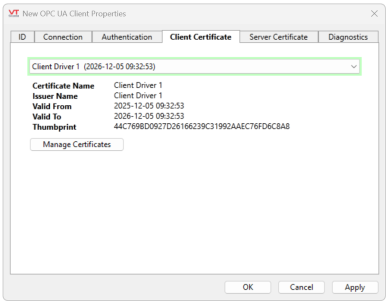
OPC UA Client Driver properties Client Certificate tab
Refer to OPC UA Support & Security for more detail on required security configuration.
Contains a 'Select a certificate...' drop-down, fields for basic information of the selected certificate and a 'Manage Certificates' button.
Use this to choose the certificate that the OPC UA Client will supply to the server for transport security. It displays only valid certificates of the appropriate extended key usage type (that is, suitable for client authentication) that are in the current user’s Trihedral OPC UA Client certificate store. That certificate store is created by the OPC UA Driver for this purpose.
OPC UA Client Driver properties Server Certificate tab
Refer to OPC UA Support & Security for more detail on required security configuration.
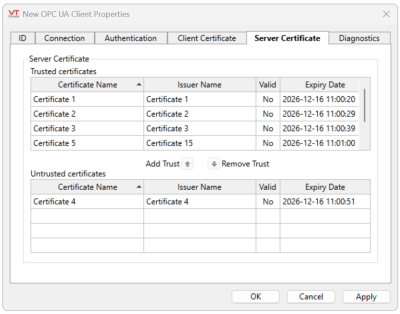
This tab holds a pair of certificate grids showing trusted and untrusted server-supplied transport security certificates, if any (See: Certificate Management UI). The certificates displayed are those in the current user’s Trihedral OPC UA Trusted and Trihedral OPC UA Untrusted certificate stores.
The server provides its certificate during establishment of a connection with the client. The OPC UA Client will only allow the connection to be established if the certificate is trusted (See Certificate Error Messages for issues that may arise).
If the server’s certificate is derived from a trusted certificate authority (in other words, there is a complete chain of trust from the server’s certificate through any intermediate certificates to the trusted certificate authority’s certificate), the certificate will be automatically trusted and not placed in either of these stores.
If the server certificate is not trusted by virtue of such a chain of trust and is not in the Trihedral OPC UA Trusted certificate store, it is automatically placed in the Trihedral OPC UA Untrusted store and appears in this tab’s Untrusted Certificates grid. From there you can elect to trust that certificate, using the Add Trust button. This will remove the certificate from the Untrusted Certificates and place it in the Trusted Certificates grid (and corresponding store).
If the OPC UA Client trusts the server’s transport certificate, via either of the above two methods, then the OPC UA Client will allow a connection to the server to be established.
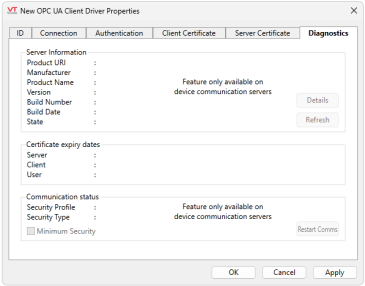
OPC UA Client Driver properties Diagnostics tab
On startup, the OPC UA Client reads certain status and other information from the server. This tab displays the most recent information and provides a button to allow the data to be refreshed. The data is only available when there is a good connection to the server.
There is also a check box that allows an unsecured, unencrypted transport connection to be made to the server (if the server permits such a connection) for debugging purposes. The state of the check box always reverts to unchecked when the driver is reloaded (typically on restart of the application). After selecting or deselecting the check box, use the Restart Driver button to cause the OPC UA Client to disconnect and reconnect to the server, thereby switching between secure and unsecured communication.
The following widgets are available to display information about your application’s OPC UA Client Driver tags:
Equipment / Status Color Indicator
