Standard Component
Integrated SCADA Application Security – More Control, Less Complexity
All the security features in the world are of no use if they are so burdensome that operators and developers avoid using them. Like all our core SCADA features, we strive to make SCADA application security management simple and scalable, while remaining infinitely configurable. Application security is managed within the standard operator interface, allowing authorized users to make changes without switching views; then instantly deploy those changes across the entire system without restarting. Best of all, VTScada does not utilize Java and is therefore unaffected by Java-based exploits.
 Security By Design (IEC-62443-4-1 ML3 Certification)
Security By Design (IEC-62443-4-1 ML3 Certification)
VTScada’s Development Environment is certified to be compliant with IEC 62443 Security For Industrial Automation And Control Systems – Part 4-1: Secure Product Development Lifecycle Requirements – Maturity Level 3 by international certification authority exida. ML3 recognizes that Trihedral’s codified procedures meet the IEC 62443 4-1 standard and are consistently being applied and improved upon.
View VTScada’s IEC 62443 4-1 ML3 Cyber Security Certificate here.
The VTScada Security Guidelines Manual
Additionally, Trihedral has developed a Security Guidelines Manual to help users harden their systems against ever evolving threats. This document provides guidance information necessary to install, commission, verify and maintain the cybersecurity certified capability of VTScada in accordance with applicable IEC 62443 cybersecurity standards. This resource is embedded in every VTScada license (including VTScadaLIGHT) and is available to everyone here.
Launch The VTScada Security Guidelines Manual
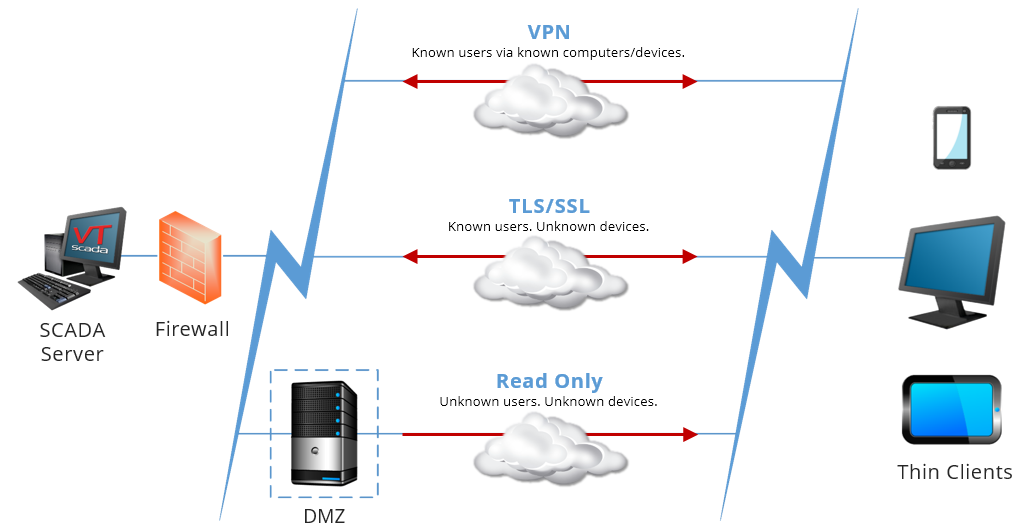
Integrated tools to support your security strategy
- Centralized account management
- Industry-standard encryption (TLS)
- Read Only Server Options
- Windows active directory support
- Immediate application wide change deployment
- OpenID Connect® for single sign-in and Two-Factor Thin Client authentication
- Supports OAuth 2.0 for SMTP and POP3 authentication
- Configuration traceability
- Card-reader support
Implementations compliant with…
- NERC/CIP (North American Electric Reliability Corporation)
- DFARS 252 (Defense Federal Acquisition Regulations Supplement)
- NIST 800 (National Institute of Standards and Technology)
- Marine reliability standards ABS, Lloyds Bureau, DNV, BV
 A Smarter Approach to Security Management
A Smarter Approach to Security Management
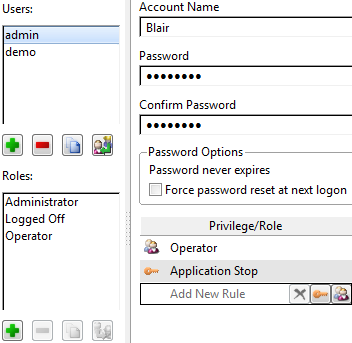
Each application includes its own security accounts and settings which control access to all parts of the application including workstations, thin clients, mobile clients, and alarm notifications. Deployed security changes are immediate and application wide. Accounts are easily copied, modified, and deleted. You can now even share accounts across multiple applications.
Rules and Roles simplify user management by replacing an ever-growing list of privileges.
- Rules combine tags, privileges, and locations to finely tune who can do what, where.
- Roles are sets of Rules corresponding to specific jobs (e.g., plant opera-tor). Quickly configure new users by adding one or more roles to an account.
Industry-Standard Encryption
The security database scheme employs the same level of encryption as online banking as does the security data exchanged between Internet Clients and Servers.
Security Protocols
In addition to TLS (Transport Layer Security) VTScada supports SMTP email servers requiring TLS (e.g., Gmail) when sending alarm notifications. USB hardware keys (dongles) are also available.
Password Protection
Configure passwords to exceed a minimum length, contain alphabet-ic, numeric, or special characters, or expire after a configurable period. Accounts can be disabled following repeated failed log-in attempts and users can be logged-out after a configurable period of inactivity.
Options for Easy Login
- Windows® Security Integration – Log on to VTScada using your Windows account. No need to manage both Windows and VTScada accounts.
- Proximity Card Readers – Log on the same way you enter a secured building. Configure Operator Notes to require authentication.
- OpenID Connect® – Provides sign-in and Two-Factor Thin Client authentication.
Enhanced Security with OpenID Connect®
Support for OpenID Connect permits integration of VTScada Security with third-party authentication servers on VTScada Anywhere Clients. Depending on your chosen authentication server, this can allow single sign-in (one password to access to many systems) and two-factor authentication (e.g., Google Authenticator or Apple Touch sensor).
IANA Registered Port
The VTScada RPC Manager automatically syncs historical data, alarm/event history, change log, user accounts, and application settings in real time across redundant servers. For maximum security and efficiency, VTScada has its own registered TCP/IP port number assigned by the Internet Assigned Numbers Authority (IANA) exclusively for RPC traffic.
Group Management
Define what information users can see in large applications. For example, if an application monitors two plants, operators from each plant can be grouped so that they see only the alarms and tags from their respective plants. A third group for managers can be set up to see information from both plants.
Share Security Accounts Across Applications
To reduce duplication and ensure consistency, accounts can now be shared across multiple applications. The security database scheme now employs military-grade encryption as does the security information exchanged between the VTScada Internet Client and Server.